
It is easy to ignore the need to protect your Data, especially for small business owners. While large businesses have an IT department, many of these small businesses do not have that luxury and count on their Internet Service Provider (ISP) to give them the tools to stay connected. Small business owners frequently rely on consumer software which lacks security that is always monitoring the connections that are coming in and out.
Lets start with our Passwords:
The first step to think about with encryption is to start with a strong password as many software systems will require a password such as encrypting a file. Decrypting it will require a password to do so and if the password is weak it does not matter if the encryption is strong since you left the door open to your data. If you use a weak password a “black hat” hacker can break the encryption and access your files which defeats the purpose of utilizing this software.
A strong password should have at least 10 or more characters. It should include a mix of uppercase, lowercase, numbers and symbols. If you need to have a password you can remember you can use a phrase. Just use a phrase that has 20 or more characters.
If after choosing your password you are still unsure that it is strong enough you can use run it through Microsoft’s free password checker. Never use a password rated less than “Strong.”
Encrypting your entire Hard Disk Drive:
Let’s assume that you already have login credentials (Username/Password) to gain access to your computer. This will not protect your data if someone steals your hard disk drive or your whole computer. They will simply need to use software to either remove the password by modifying the SAM file or in the case of a Macintosh computer simply popping in an OS installation disk and just simply click to change the password or remove it.
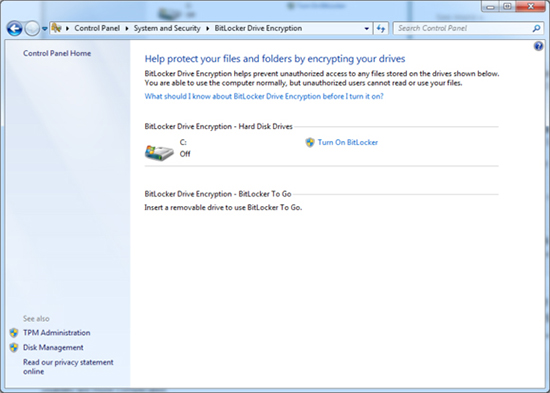
Microsoft’s BitLocker software makes setting up full-disk encryption in Windows incredibly easy, as long as your computer meets the following two criteria:
1. You have the Ultimate or Enterprise version of Windows 7 or Vista, or the Pro or Enterprise version of Windows 8.
2. Your computer has a TPM (Trusted Platform Module) chip.
The easiest way to see if your computer has a TPM chip is simply to attempt to enable BitLocker. Windows will let you know if you don’t have one.
To enable BitLocker, go to Control Panel>System and Security>BitLocker Drive Encryption, or do a search for “BitLocker” in Windows 8. In the BitLocker menu, click “Turn on BitLocker” next to the drive(s) you wish to encrypt. It’s as easy as that.
If your PC does not meet the requirements for BitLocker, you can still use TrueCrypt or DiskCryptor for free full-disk encryption.
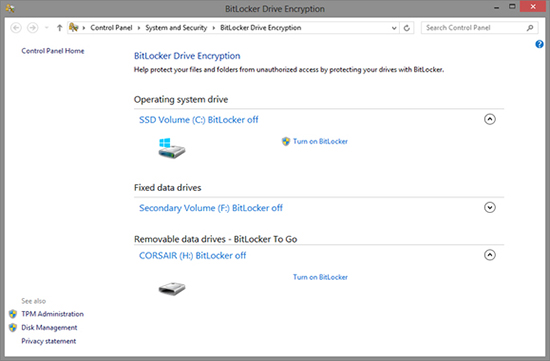
Encrypting your external Hard Drives or USB Thumb Drives:
To fully encrypt thumb drives as well as USB Hard Drives, you can utilize “BitLocker to Go” encryption in Windows 8. It is especially designed for removable media devices.
All you need to do is to attach your removable media to your computer and once again go to the BitLocker menu. at the bottom of the menu, you will see “Bitlocker To Go” Section, where you can click and turn on Bitlocker next to the device.
Encrypting your external Hard Drives or USB Thumb Drives:
To fully encrypt thumb drives as well as USB Hard Drives, you can utilize BitLocker to Go encryption in Windows 8. Wish is especially designed for removable media devices.
All is needed is to attach your removable media to your computer and once again go to the BitLocker menu. at the bottom of the menu, you will see “Bitlocker To Go” Section, where you can click and Turn on Bitlocker next to the device.
Encrypting your Drop Box:
If anyone in your company or yourself use Drop Box, you will be happy to know that those popular cloud storage services already encrypt your data, protecting it while it is being transmitted, as well as when it is in their computer servers. The sad part is those services also hold the decryption keys which mean that they can also decrypt your files if, for instance, law enforcement directs them to do so.
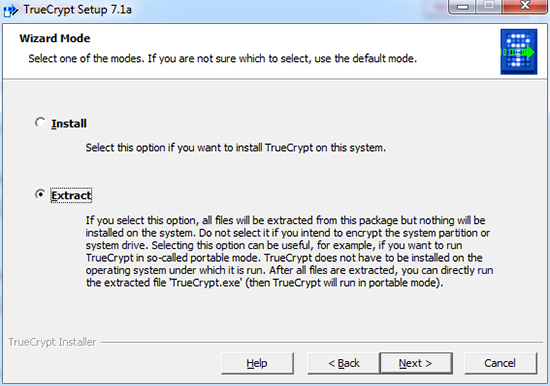
If you have sensitive data, you can use a second layer of protection to keep it safe from any prying eyes. The easy and straightforward way to do this is to utilize TrueCrypt to create an encrypted volume inside of your Dropbox. If you have the need to access the data in other computers, you can use a portable version of TrueCrypt. Simply upload it to your DropBox and use it every time you are on a different computer. To do so, run the TrueCrypt installer. During the installation, choose the Extract option and choose to put the extracted files in your Dropbox or other cloud storage.
Encrypting your email:
Your email messages can contain sensitive information, which makes them a candidate for encryption. If you are using Outlook, keeping your E-mail’s it is easy.
Outlook encryption is not password-based. Instead, anyone who wants to use cryptographic security features in Outlook receives a digital certificate, which serves to automatically encrypt and decrypt messages. Before two users can send each other encrypted messages, they must share their certificates by sending each other digitally signed messages. It sounds sort of complicated, but the process is actually straightforward, and takes only a few moments. To set up Outlook for encrypted messaging, follow the steps in the official Microsoft guide.
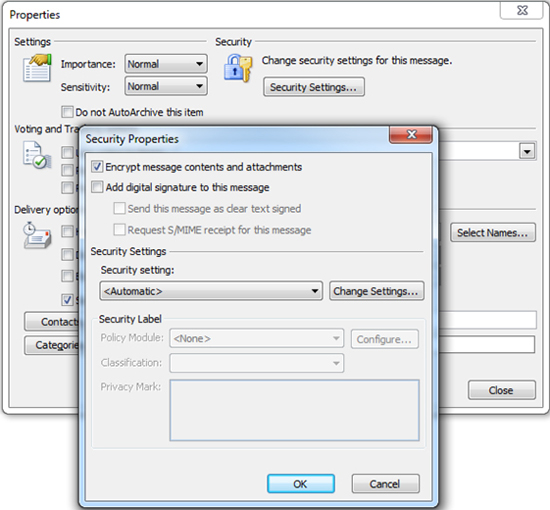
Once you have received and exchanged digital IDs, you can send an encrypted message by opening the new message window, clicking Options>More Options>Security Settings, and checking the box for “Encrypt message contents and attachments”.
Sounds a bit complicated?
![]()
Simply start using Gmail before you would have to go and change some settings to enable the SSL. Now you can simply log in and start using your Gmail without the need to enable this. Session-long HTTPS has been an official option for Gmail users since 2008 (and unofficial for much longer), but Google says it hesitated turning it on for all since the encryption does slow down the service.
Surfing the Web in total Anonymity:

There are many ways to complete this task. One of my personal favorites is using the TOR browser. It utilizes thousands of relays on its network and its intended to protect the personal privacy of users, as well as their freedom and ability to conduct confidential business by keeping their internet activities from being monitored.
Here is a video going in depth into this great browser and how its growing in users.
